IT Hardware Auditing Service England
French Bank Offices Located in South England
“A longstanding client required assistance in verifying their IT Hardware estate.”
The Problem
With the IT equipment being situated over 2 sites and an element of staff being predominantly mobile or home-based, there are few opportunities to capture everyone within the standard office environment.
Added to this an out of date CMDB system, along with a change in the working practices of the client, the requirement for an IT Hardware Auditing Service was there to be seen but the chance of capturing the entire estate was the first problem to overcome.
Challenges
With all IT Hardware Audits, planning and communication is key to successful delivery. We provided each site with a date range to inform them of our attendance to complete the Physical IT Hardware Audit aspect, this gave the users around a months notice to notify those concerned of their known absence.
Added to the Physical presence, we devised a process for capturing the known absentees, mobile users and home workers and their associated devices to ensure an acceptable level of completeness was achieved.
Solution
A team was deployed to each site for a set period of days to capture the fixed devices within each location and to capture all IT Hardware of users who were within the sites on these days.
A week prior to these visits and for a 2-week window afterwards we constructed an online secure webpage which was designed and branded to represent the client’s image. This allowed all mobile users and remote workers to upload their details and be part of the larger IT Hardware Auditing exercise. With the changing working methodology, this format was vital in the delivery of this audit.
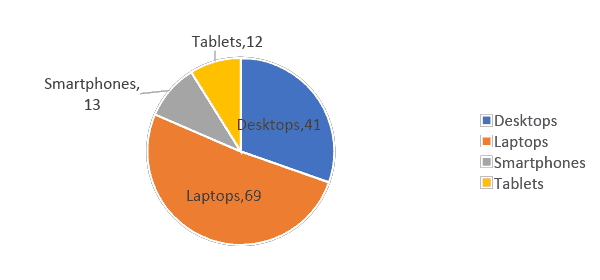
Additional Devices Found
As part of the exercise, 135 devices were identified as not being within the existing CMDB system. This lead to further complications for the management of the IT Hardware System.
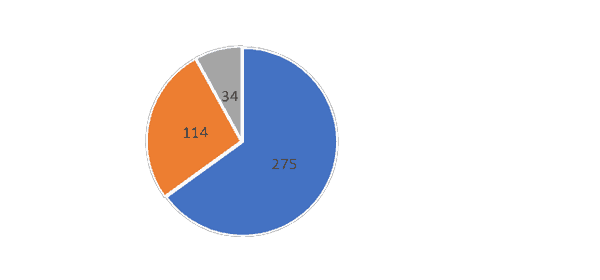
User Location
We were also able to provide the client with a full breakdown of users who have been captured as part of the IT Hardware Audit exercise by location.
Furthermore, by using an agreed user list we were also able to identify those who have not been captured and a further targeted remote audit was implemented to ensure all these users were incorporated into the final submitted results.